Online protection company Proofpoint warns that new, sophisticated malware impersonating Google Chrome and Microsoft has the potential to steal money from Windows device owners. This malware is being used by several groups of cybercriminals, including some known for sending spam emails that can infect computers. malware or ransomware.
This malware tricks users into downloading harmful code by posing as fake updates in internet browsers such as Chrome. Once the code is stored on your computer, hackers can access your cryptocurrency, sensitive files, and personal information.
Get security alerts and expert tips – sign up for CURT's newsletter here – CYBERGUY Report

Microsoft Laptop (Microsoft) (Kurt “Cyberguy” Knutsson)
How does fake update malware work?
proof point Although it confirmed large-scale distribution of the malware this month, the online protection company believes the campaign has been ongoing since March 2024. This malware disguises itself as fake Google Chrome, Word and OneDrive errors to force users to download harmful code. These errors prompt visitors to click a button to copy the PowerShell “Edit” to the clipboard, then paste it into the Run dialog or PowerShell prompt and run it.
“While an attack chain requires significant user interaction to be successful, social engineering is clever enough to present someone with both a real problem and what appears to be a solution, which can lead users to take action without considering the risks,” Proofpoint said. warns.
When the PowerShell script runs, it verifies that the device is a valid target. It then downloads more payload. These steps include clearing the DNS cache, removing clipboard content, displaying fake messages, and downloading other remote PowerShell scripts.
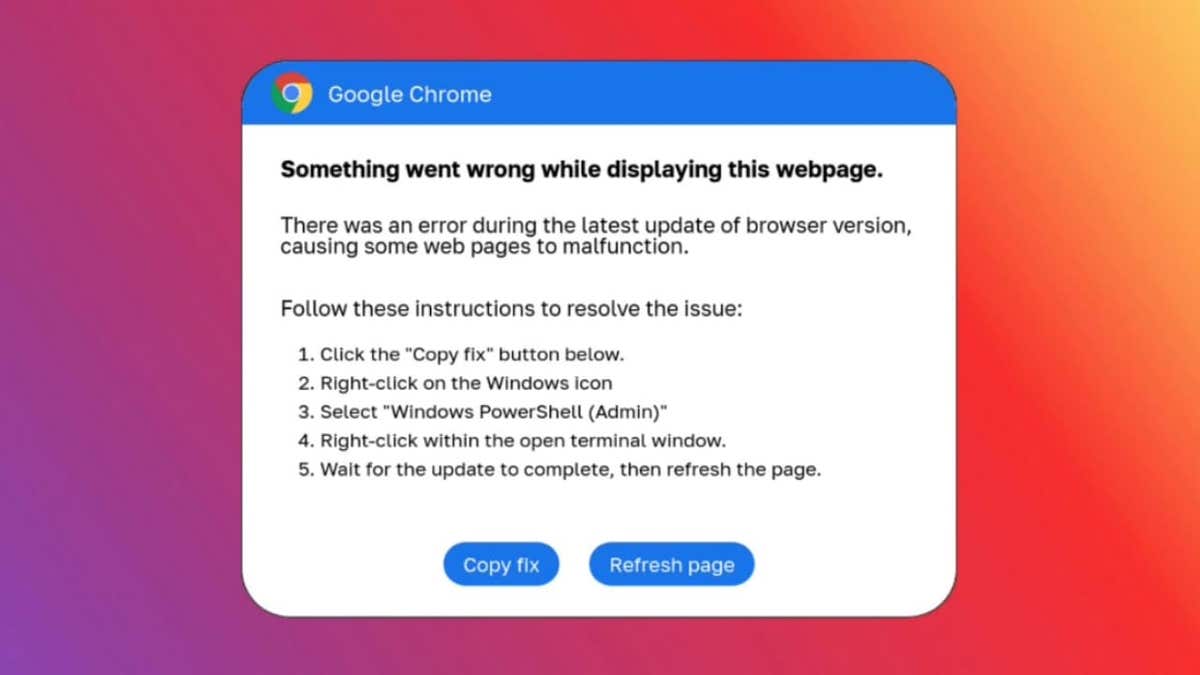
ClickFix Error Message (Proof) (Kurt “Cyberguy” Knutsson)
BEST Antivirus for PC, MAC, IPHONE and Android – CYBERGUY PICKS
Cryptocurrency theft
This second script verifies that the information stealer is running on the virtual machine before downloading it. Once everything is in place, the hacker can access the victim's cryptocurrency. The scheme redirects the victim's funds to the hackers instead of the intended recipient.
Alternative Attack Method: Email Bait
Proofpoint points out that malicious actors use another method called “email bait” to install harmful software. Emails that appear to be business or corporate-related typically contain HTML files similar to Microsoft Word. These emails prompt users to install the “Word Online” extension to view the document properly.
Similar to the method above, the user is prompted to open PowerShell and copy the malware. Proofpoint says the deceptive “campaign” is widespread. “The campaign included more than 100,000 messages and targeted thousands of organizations around the world,” according to the company.
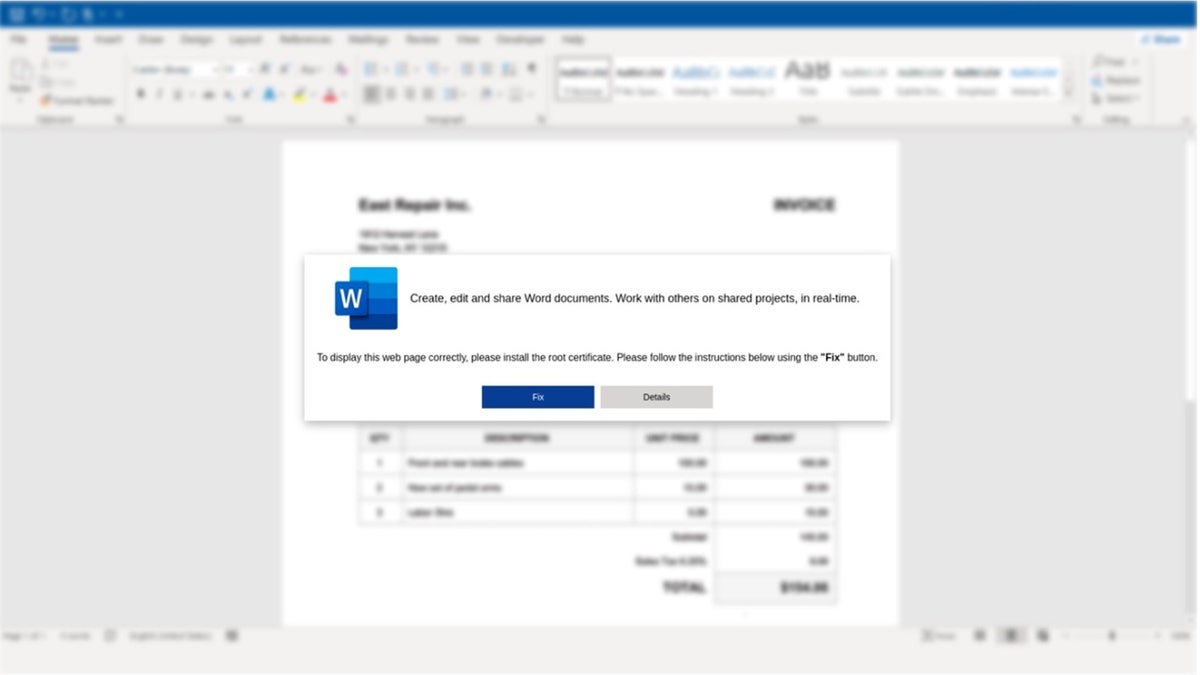
HTML attachment with instructions on how to copy and paste PowerShell leading to installation of malware (Proofpoint) (Kurt “Cyberguy” Knutsson)
Prevent nearby snoops from hearing your voicemail with these quick tips
5 ways to protect yourself from harmful software
Fake Chrome and Microsoft Word malware creates a sense of urgency, tricking users into clicking links and unknowingly compromising their devices. There are several steps you can take to protect yourself from this malware.
1) You must have strong antivirus software. The best way to protect yourself from clicking on malicious links that install malware that can access your personal information is to install antivirus protection on all your devices. It may also alert you to phishing emails or ransomware scams. Choose your winner for the best antivirus protection of 2024. Windows, Mac, Android and iOS devices.
2) Use a VPN: Consider using a VPN to prevent tracking and potentially identify your location on the websites you visit. Many sites can read your IP address, and depending on your privacy settings, they may see the city you live in. A VPN spoofs your IP address to show an alternate location. To find the best VPN software, read our expert reviews of the best VPNs for browsing the web privately on your computer. Windows, Mac, Android and iOS devices.
3) Monitor your account: Regularly review your bank statements, credit card statements, and other financial accounts for unauthorized activity. If you see any suspicious transactions, report them immediately to your bank or credit card company.
4) Raise a fraud alert: Contact one of the three major credit reporting agencies (Equifax, Experian, or TransUnion) and request that a fraud alert be placed on your credit file. This makes it more difficult for identity thieves to open new accounts in your name without verification.
5) Enable two-factor authentication: enable double element proof Whenever possible. This adds an additional layer of security by requiring a second form of verification, such as a code sent to your phone, in addition to your password.
How to remove personal data from the Internet
Kurt’s Key Takeaways
Hackers have cleverly designed malware that prompts you to install it on your device. This malware specifically targets Windows users, and Windows devices have been shown to be more vulnerable to this kind of attack. Microsoft recently acknowledged the following: Wi-Fi driver flaw in Windows could allow hackers to hijack your PC All you need to do is be on the same Wi-Fi network. It's important to be careful when browsing online or connecting to public Wi-Fi.
How do I check the authenticity of software before downloading and installing it on my device? Please let us know by sending a letter to: Cyberguy.com/Contact Us.
Subscribe to the free CyberGuy Report newsletter for more tech tips and security alerts. Cyberguy.com/Newsletter.
Ask Kurt a question or let him know what story you'd like us to cover..
Follow Kurt on his social channels:
Answers to CyberGuy's most frequently asked questions:
Copyright 2024 CyberGuy.com. All rights reserved.