Last November, we launched the Secure Future Initiative (SFI) to prepare for the increasing scale and risk of cyberattacks. SFI brings together all parts of Microsoft to strengthen cybersecurity protection across the company and products.
Since then, the threat landscape has continued to evolve rapidly and we have learned a lot. The Department of Homeland Security's Cyber Safety Review Board (CSRB)'s recent investigation into the Storm-0558 cyberattack in July and the Midnight Blizzard attack reported in January highlights the seriousness of the threats our company and customers face.
Microsoft plays a central role in the world's digital ecosystem, and with that comes the critical responsibility of earning and maintaining trust. femaleI have and will continue to do more..
we are At Microsoft, security is our top priority.—Beyond all other functions. We are expanding the scope of SFI by incorporating recent recommendations from the CSRB and learnings from Midnight Blizzard to ensure that our cybersecurity approach remains robust and adaptive to the evolving threat landscape.
We will mobilize the expanded SFI principles and goals across Microsoft, and this will be one dimension of our hiring decisions. It will also instill a sense of responsibility based on a portion of the company's senior leadership team's compensation for security planning and achievement of milestones.
Below are details that demonstrate the seriousness of our work and commitment.
Expanding the SFI approach and scope
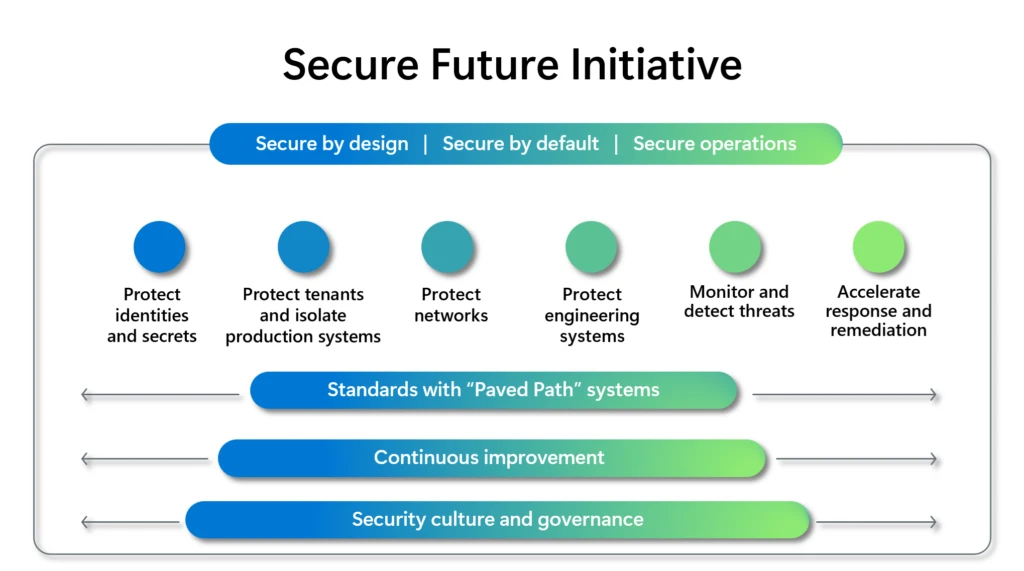
We have evolved our security approach and our future work will be guided by: Three Security Principles:
- Secure design: Security is a top priority when designing a product or service.
- Default Security: Security protections are enabled and applied by default, require no additional effort, and are not optional.
- Security Operations: Security controls and monitoring will continue to improve to address current and future threats.
We are expanding our goals and actions to: 6 Priority Security Principles Provides visibility into execution details.
1. Protect your identity and confidentiality
Reduce the risk of unauthorized access by implementing and enforcing the highest standards across all identity and secrets infrastructure, user and application authentication and authorization. As part of this, we are taking the following actions:
- Protect your identity infrastructure signatures and platform keys by rapidly and automatically rotating through hardware storage and protection, such as hardware security modules (HSMs) and confidential computing.
- Enforce identity standards and drive adoption by using standard SDKs in 100% of your applications.
- User accounts are 100% protected through securely managed, anti-phishing multi-factor authentication.
- Make sure your application is 100% protected with system managed credentials (e.g. managed identity and managed certificate).
- Ensure your ID tokens are 100% protected with stateful and durable verification.
- Adopts a more granular split of identity signing keys and platform keys.
- Make sure your identity and public key infrastructure (PKI) system is ready for the post-quantum crypto world.
2. Protect tenants and isolate production systems.
Minimize impact by protecting all Microsoft tenants and production environments with consistent, best-in-class security practices and strict isolation. As part of this, we are taking the following actions:
- Maintain your tenant's security posture and commercial relationships by removing all obsolete, outdated or legacy systems.
- Microsoft-acquired and employee-created tenants, commerce accounts, and tenant resources are 100% protected according to security best practice standards.
- Manage your Microsoft Entra identity applications with 100% high and consistent security.
- 100% eliminate lateral identity movement pivots between tenants, environments, and clouds.
- 100% of your applications and users consistently enforce least-privilege access.
- Ensures that only secure, managed, and healthy devices are granted access to your Microsoft tenant.
3. Network protection
Secure Microsoft production networks and implement network isolation of Microsoft and customer resources. As part of this, we are taking the following actions:
- Provides 100% protection for Microsoft production networks and systems connected to your network by improving isolation, monitoring, inventory, and security operations.
- We apply network isolation and micro-segmentation to 100% of Microsoft production environments to create an additional layer of defense against attackers.
- We help customers easily secure their networks and network isolate resources in the cloud.
4. Engineering system protection
Protect your software assets and continuously improve code security through governance of your software supply chain and engineering systems infrastructure. As part of this, we are taking the following actions:
- Build and maintain an inventory of 100% of the software assets used to deploy and operate Microsoft products and services.
- Access to source code and engineering system infrastructure is 100% protected through zero trust and least-privilege access policies.
- Source code deployed to Microsoft production environments is 100% protected using security best practices.
- Protect your development, build, test, and release environments with 100% standardized and managed pipelines and infrastructure isolation.
- Secure your software supply chain to protect your Microsoft production environment.
5. Threat monitoring and detection
Comprehensively detect and automatically detect threats to Microsoft production infrastructure and services. As part of this, we are taking the following actions:
- Maintain up-to-date inventory across Microsoft production infrastructure and services.
- We retain 100% of our security logs for at least 2 years and provide appropriate logs to our customers for 6 months.
- 100% of security logs are accessible from a central data lake, enabling efficient and effective security investigation and threat hunting.
- Automatically detect and quickly respond to anomalous access, behavior, and configuration across Microsoft production infrastructure and services.
6. Accelerate response and resolution
Prevent exploitation of discovered vulnerabilities by external and internal entities through comprehensive and timely remediation. As part of this, we are taking the following actions:
- Accelerated response reduces the time it takes to mitigate high-severity cloud security vulnerabilities.
- Transparency of mitigated cloud vulnerabilities through the adoption and release of the Common Weakness Enumeration™ (CWE™) and Common Platform Enumeration™ (CPE™) industry standards for high severity common vulnerabilities and exposures (CVEs) affecting the cloud. Raise it.
- Improve the accuracy, efficiency, transparency, and speed of your public messaging and customer engagement.
These goals span across the areas of security culture, cybersecurity best practices, audit logging practices, and digital identity, along with lessons learned from the Midnight Blizzard incident, all four CSRB recommendations for Microsoft, and twelve recommendations for cloud service providers (CSPs). directly corresponds to . Standards, guidelines, transparency.
We are achieving this goal through a new level of alignment with a new operating model that aligns leaders and teams with the six SFI principles to drive security holistically and break down traditional silos. Key leaders are driving integrated, cross-company engineering practices across the Engineering Vice President (EVP) and are doing this in waves. This engineering wave involves teams across Microsoft Azure, Windows, Microsoft 365, and Security, with additional product teams being integrated into the process each week.
There is much more work to be done, but progress has been made in implementing SFI priorities. For example, we've implemented automatic enforcement of multi-factor authentication by default for more than one million Microsoft Entra identity tenants within Microsoft, including tenants for development, testing, demo, and production. We have eliminated or reduced our application audience by removing 730,000 apps to date across production and enterprise tenants that are past their lifecycle or do not meet current SFI standards. We've expanded logging to provide deeper visibility to our customers. And we recently announced significant changes to our response process. We are now publishing root cause data for Microsoft CVEs using the CWE™ industry standard.
Comply with standards with paved path systems
The paved path is based on lessons learned and examples drawn from experience, such as how to optimize the productivity of software development and operations and how to achieve regulatory compliance (e.g., software BOM, Sarbanes-Oxley Act, General Data Protection Regulation, etc.) This is a case. ) and how to eliminate entire categories of vulnerabilities and mitigate the associated risks. The paved path becomes the standard when adoption significantly improves developer or operational experience, security, quality, or compliance.
With SFI, we explicitly define standards for each of the six security principles, and compliance with these standards is measured by Objectives and Key Results (OKRs).
Driving continuous improvement
The Secure Future Initiative helps all of Microsoft implement the changes necessary to deliver security as a top priority. Our company culture is based on a growth mindset that fosters a spirit of continuous improvement. We continually seek feedback and new perspectives to adjust our approach and progress. We will apply what we learn from security incidents back to our security standards and operationalize these learnings into a paved path to enable security design and operations at scale.
Establishing new governance
We are also taking major steps to improve our security governance, including several organizational changes and additional oversight, controls and reporting.
Microsoft is implementing a new security governance framework led by the Chief Information Security Officer (CISO). The framework introduces a partnership between the engineering team and the newly created deputy CISO, who are jointly responsible for overseeing SFI, managing risk, and reporting progress directly to the senior leadership team. Progress is reviewed weekly through executive forums and quarterly by the board of directors.
Finally, given the importance of threat intelligence, we are leveraging nation-state actor and threat hunting capabilities to our CISO organization.
Instilling a security-first culture
Culture can only be strengthened through everyday actions. Security is a team sport and is best achieved when organizational boundaries are overcome. The EVP of Engineering works closely with SFI key leaders to host extensive weekly and monthly operational meetings that include all levels of management and senior individual contributors. These meetings are where we drill down and continually improve security as it relates to what we collectively offer to our customers. It is through this top-down, end-to-end problem-solving process that security thinking becomes ingrained in our daily behavior.
Ultimately, Microsoft operates on trust, and we must earn and maintain that trust. As a global provider of software, infrastructure and cloud services, we feel a deep sense of responsibility to do our part to keep the world safe. Our commitment is to continuously improve and adapt to evolving cybersecurity requirements. This is a number one job for us..